Key Generation Algorithm In Cloud Computing
- Key Generation Algorithm In Cloud Computing Software
- Key Generation Algorithm In Cloud Computing System
- Key Generation Algorithm In Cloud Computing Science
- Key Generation Algorithm In Cloud Computing Technology
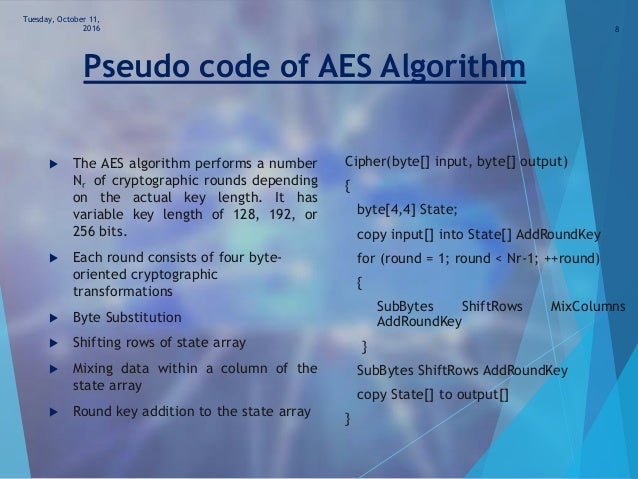
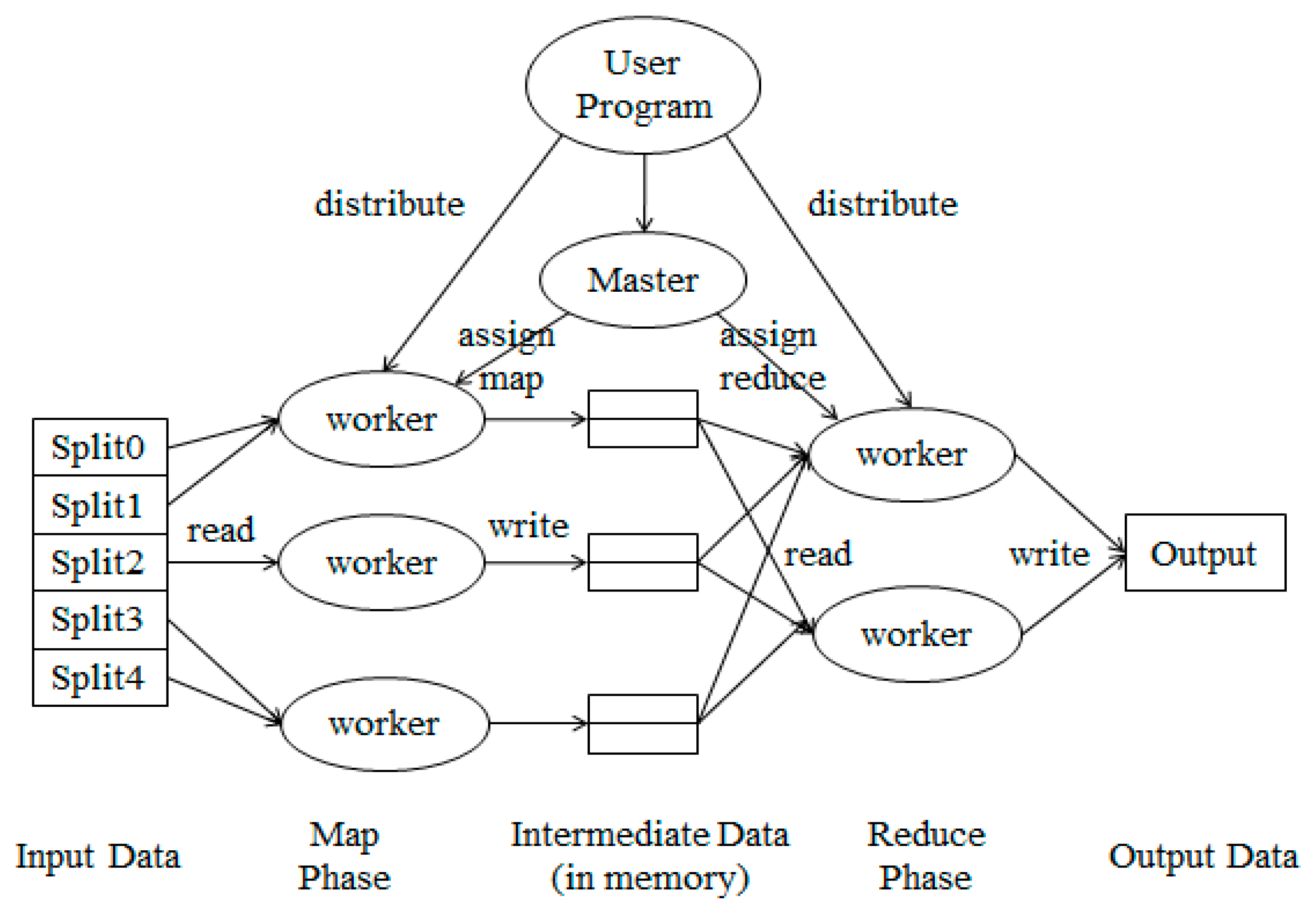
Oct 31, 2012 Identity Based Encryption (IDE): In IDE, one’s publicly known identity (ex. Email address) is being used as his/her public key where ascorresponding private key is generated from the known identity.IDE encryption scheme is a four algorithms/steps scheme where the algorithms are i. Setup Algorithm ii.Key (private key) Generation Algorithm iii. Thus, this paper implements a double stage encryption algorithm for multimedia content security using random key generation approach. The first stage encrypted multimedia content into ciphertext-1. Key generation. The keys for the RSA algorithm are generated in the following way: Choose two distinct prime numbers p and q. For security purposes, the integers p and q should be chosen at random, and should be similar in magnitude but differ in length by a few digits to make factoring harder. Cloud computing, distributed data, security, RSA algorithm: INTRODUCTION: Cloud computing denotes sharing of resources rather than having local servers to handle applications. It provides services to servers, storage and applications over the internet. And this cloud computing environment is used by all small and large company users.
Davinci resolve activation codes. The new edit selection mode unlocks functionality previously only available via the audio editor on the full Fairlight console, so editing is much faster than before. Bouncing lets customers render a clip with custom sound effects directly from the Fairlight timeline. New scalable waveforms let users zoom in without adjusting the volume. In addition, the edit selection mode makes adding fades, cuts and even moving clips only a mouse click away.
This class provides the functionality of a secret (symmetric) key generator.Key Generation Algorithm In Cloud Computing Software
Key generators are constructed using one of the getInstance class methods of this class.
KeyGenerator objects are reusable, i.e., after a key has been generated, the same KeyGenerator object can be re-used to generate further keys.
There are two ways to generate a key: in an algorithm-independent manner, and in an algorithm-specific manner. The only difference between the two is the initialization of the object:
Key Generation Algorithm In Cloud Computing System
- Algorithm-Independent Initialization
All key generators share the concepts of a keysize and a source of randomness. There is an
initmethod in this KeyGenerator class that takes these two universally shared types of arguments. There is also one that takes just akeysizeargument, and uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation), and one that takes just a source of randomness.Why is it that other programs take so much and is so fast? For you to use this tool you just need to have a computer with a wireless adapter or a wireless pen, that nowadays any portable computer has. Most programs take hours and hours and hours, let alone days to discover a simple password, but now you ask. Free download wifi password key generator v2.5.
Since no other parameters are specified when you call the above algorithm-independent
initmethods, it is up to the provider what to do about the algorithm-specific parameters (if any) to be associated with each of the keys. - Algorithm-Specific Initialization
For situations where a set of algorithm-specific parameters already exists, there are two
initmethods that have anAlgorithmParameterSpecargument. One also has aSecureRandomargument, while the other uses the SecureRandom implementation of the highest-priority installed provider as the source of randomness (or a system-provided source of randomness if none of the installed providers supply a SecureRandom implementation).
In case the client does not explicitly initialize the KeyGenerator (via a call to an init method), each provider must supply (and document) a default initialization.
Key Generation Algorithm In Cloud Computing Science
Every implementation of the Java platform is required to support the following standard KeyGenerator algorithms with the keysizes in parentheses:
Key Generation Algorithm In Cloud Computing Technology
- AES (128)
- DES (56)
- DESede (168)
- HmacSHA1
- HmacSHA256