Generate Pgp Key On Mac
by Radu Raicea
Apr 23, 2018 PGP is the gold standard for encrypted communication and has been used by everyone from nuclear activists to criminals since its invention in 1991. While the execution is complex, the concept and usage is simple. This article shows how it works and how you can get started. PGP Everywhere emphasizes ease of use and convenience. The option to use Touch ID instead of entering your passphrase allows you to encrypt and decrypt in places where it would be too inconvenient and cumbersome otherwise, like texting or instant messaging. GENERATE KEYS. PGP Everywhere offers the ability to generate new key pairs. PGP Private Key Save your PGP private key in a file on your computer and keep it as confidential as possible. Use copy & paste to a text editor such as Notepad to save your PGP key. If you are on version 2.1.17 or greater, paste the text below to generate a GPG key pair. $ gpg -full-generate-key; If you are not on version 2.1.17 or greater, the gpg -full-generate-key command doesn't work. Paste the text below and skip to step 6. $ gpg -default-new-key-algo rsa4096 -gen-key; At the prompt, specify the kind of key you. May 15, 2016 How to create new keys. How to create new keys. Skip navigation. Generating OpenPGP keys using Kleopatra on Windows. How to manage File Transfer PGP. To generate your keys, you need to install GnuPG (aka GPG). GPG is a free software alternative to the closed source commercial PGP. To install GPG with Homebrew, it’s as simple as: brew install gpg pinentry-mac. SiteGround uses key pairs for SSH authentication purposes, as opposed to plain username and password. More information on SSH keys is available here. You can generate an SSH key pair in Mac OS following these steps: Open up the Terminal by going to Applications - Utilities - Terminal.
Sending sensitive information through the internet is always nerve-racking. What if somebody else sees the bank information I’m sending? Or even those dank memes that should not be spoken of?
Fortunately, there’s a pretty good solution to this problem: Pretty Good Privacy (PGP).
A software engineer named Phil Zimmermann created PGP back in 1991. He was an anti-nuclear activist, and wanted a way to transfer information securely over the Internet.
Zimmermann got into trouble with the US government in 1993 because PGP travelled international waters and reached a vast number of countries around the globe, violating US export restrictions for cryptographic software.
Today, PGP is “owned” by Symantec, but OpenPGP, an e-mail encryption standard, is implemented by multiple software.
You might also hear a lot about GPG. It is another software tool that implements the OpenPGP standard.
How does PGP actually work?
PGP is very easy to understand, on the surface. Imagine you want to send your credit card information to a friend and you write it on a piece of paper. You then put the paper in a box and send it by mail.
A thief can easily steal the box and look at the paper that contains your credit card information. What could you do instead?
You decide to put a key lock on the box, but you realize that you have to send the key along with the box. That’s no good.
What if you meet your friend in person to share the key beforehand? That could work, right? It could, but then both of you have a key that allows to unlock the box. You, as the sender, will never need to open the box again after closing it. By keeping a copy of a key that can unlock the box, you are creating a vulnerability.
Finally, you found just the right solution: you’ll have two keys. The first key will only be able to lock the box. The second key will only be able to open the box. That way, only the person who needs to get the content of the box has the key that allows them to unlock it.
This is how PGP works. You have a public key (to lock/encrypt the message) and a private key (to unlock/decrypt the message). You would send the public key to all your friends so that they can encrypt sensitive messages that they want to send to you. Once you receive an encrypted message, you use your private key to decrypt it.
A Brief Example
There are plenty of software tools that implement the OpenPGP standard. They all have different ways of setting up PGP encryption. One particular tool that works very well is Apple Mail.
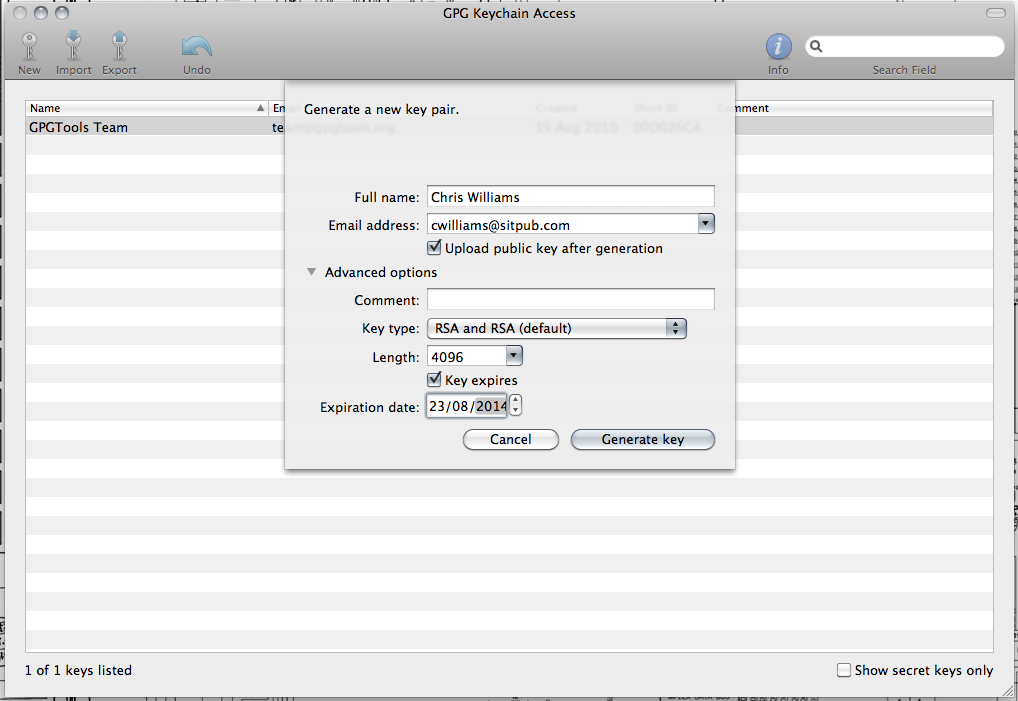
If you are using a Mac computer, you can download the GPGTools. This application will generate and manage your public and private keys. It also integrates automatically with Apple Mail.
Once the keys are generated, you will see a lock icon in the subject line, when composing a new message in Apple Mail. This means that the message will be encrypted with the public key you’ve generated.
After sending the e-mail to someone, it will look like this. They will not be able to see the content of the e-mail until they decrypt it using the private key.
Note that PGP encryption does not encrypt the subject line of an e-mail. Never put any sensitive information in the subject line.
If you are using software that automatically decrypts the message using your private key, like Apple Mail, it will look something like this: Free steam cd key generator.
In summary…
- Pretty Good Privacy (PGP) allows you to send files and messages securely over the Internet
- PGP generates a public key (to encrypt messages) and a private key (to decrypt messages)
- OpenPGP is an e-mail encryption standard
- GPG is an open-source implementation of OpenPGP
- You can find a brief list of software that have PGP capability here
References
How To Generate Pgp Key
For more updates, follow me on Twitter.
Generate Pgp Key Mac
Pretty Good Privacy (PGP) is a data encryption and decryption computer program that provides cryptographic privacy and authentication for data communication. PGP is often used for signing, encrypting, and decrypting texts, e-mails, files, directories, and whole disk partitions and to increase the security of e-mail communications. It was created by Phil Zimmermann in 1991. PGP and similar software follow the OpenPGP standard (RFC 4880) for encrypting and decrypting data. Source: Wikipedia
Create Pgp Keys
This site only provides a simple, safer and easy-to-use tool for people who want to generate a pair of PGP keys or more. Today, some common methods for generating keys still involve going to a command prompt of a Linux/Unix machine and using the GPG utility, or installing a PGP compatible application on your desktop, so I wanted to provide an easier way to generate keys. None of this would be possible without the awesome open source software that I'm using which is KeyBase's awesome JavaScript implementation of PGP (kbpgp). While for file saving capabilities, I am using Eli Grey's wonderful FileSaver.js interface.
Esxi license key free. Activation key for vCenter, vSphere 6.5. By groot February 23, 2018 Network Security 23 Comments. Fllowing are the activation key enterprise license for vCenter and vSphere 6.5: This license isn’t use for commercial purposes. Please buy a license if you can! VCenter: 0A0FF-403EN-RZ848-ZH3QH-2A73P.
Free Pgp For Mac
This site is open source and the source code are available on GitHub under MIT License. If you have any inquiry or problem, you may create an issue here.